Difference between revisions of "Oauth"
Wesley Chen (talk | contribs) (Add new property for OAuth plugin, reformat page) |
|||
| (2 intermediate revisions by one other user not shown) | |||
| Line 1: | Line 1: | ||
| − | + | =Introduction= | |
OAuth is one of the multiple ways you can authenticate users to 3forge AMI. The 3forge AMI OAuth Plugin makes it easy to integrate AMI with any OAuth based identity manager. It provides a simple standard authentication mechanism and allows you to build access control into your 3forge AMI Layouts. | OAuth is one of the multiple ways you can authenticate users to 3forge AMI. The 3forge AMI OAuth Plugin makes it easy to integrate AMI with any OAuth based identity manager. It provides a simple standard authentication mechanism and allows you to build access control into your 3forge AMI Layouts. | ||
| Line 7: | Line 7: | ||
| − | + | =OAuth Quickstart= | |
| − | + | ||
Prerequisites: | Prerequisites: | ||
<ol><li>Find out your identity provider and ensure it allows for OAuth 2.0 Authentication. You will need to know the identity provider url. | <ol><li>Find out your identity provider and ensure it allows for OAuth 2.0 Authentication. You will need to know the identity provider url. | ||
| Line 51: | Line 51: | ||
oauth.refresh.token.endpoint=/refreshTokenEndpoint | oauth.refresh.token.endpoint=/refreshTokenEndpoint | ||
| + | |||
| + | |||
| + | <strong># Properties related to refresh tokens, redirect uri and scope are optional, by default are set to null</strong> | ||
| + | |||
| + | oauth.refresh.redirect.uri=/refreshRedirectUri | ||
| + | |||
| + | oauth.refresh.scope=/refreshScope | ||
| + | |||
| + | oauth.refresh.client.id=/refreshClientId | ||
| + | |||
| + | oauth.refresh.client.secret=/refreshClientSecret | ||
| Line 87: | Line 98: | ||
| − | + | =OAuth Full Properties List= | |
| Line 139: | Line 150: | ||
|- | |- | ||
| <span style="color:#3c78d8">OPTIONAL</span> <br /> Enables Debugging Mode || oauth.debug=true | | <span style="color:#3c78d8">OPTIONAL</span> <br /> Enables Debugging Mode || oauth.debug=true | ||
| + | |- | ||
| + | | <span style="color:#3c78d8">OPTIONAL</span> <br /> Disables certificate validation (for ssl) || oauth.validate.certs=false | ||
|} | |} | ||
| Line 144: | Line 157: | ||
| − | + | =Creating your own AMI OAuth Plugin= | |
The AMI OAuth plugin handles authorization code and access token requests that are needed for Authenticating to AMI. By extending the 3forge AMI OAuth plugin, you can create your own Ami OAuth Plugin if you have custom requirements for access control or entitlements. | The AMI OAuth plugin handles authorization code and access token requests that are needed for Authenticating to AMI. By extending the 3forge AMI OAuth plugin, you can create your own Ami OAuth Plugin if you have custom requirements for access control or entitlements. | ||
| Line 150: | Line 163: | ||
There are three main components to the 3forge AMI OAuth Plugin: buildAuthRequest, processResponse, and createAmiUserSSOSession. | There are three main components to the 3forge AMI OAuth Plugin: buildAuthRequest, processResponse, and createAmiUserSSOSession. | ||
| − | + | ==Main Components of the 3forge AMI OAuth Plugin== | |
The <strong>buildAuthRequest </strong>method is responsible for creating the url for the Authorization Code request. | The <strong>buildAuthRequest </strong>method is responsible for creating the url for the Authorization Code request. | ||
| Line 161: | Line 174: | ||
| − | + | ==Diagram of the 3forge AMI OAuth Plugin== | |
| Line 167: | Line 180: | ||
| − | + | ==Example Java Code== | |
<syntaxhighlight lang="java" line="1"> | <syntaxhighlight lang="java" line="1"> | ||
| Line 261: | Line 274: | ||
| − | + | ==Example Configuration== | |
sso.plugin.class=com.company.3forge.AmiWebOAuthPluginSample | sso.plugin.class=com.company.3forge.AmiWebOAuthPluginSample | ||
Latest revision as of 03:27, 13 February 2024
Introduction
OAuth is one of the multiple ways you can authenticate users to 3forge AMI. The 3forge AMI OAuth Plugin makes it easy to integrate AMI with any OAuth based identity manager. It provides a simple standard authentication mechanism and allows you to build access control into your 3forge AMI Layouts.
Go to Section 2 OAuth Quickstart to quickly get started with using the OAuthPlugin.
OAuth Quickstart
Prerequisites:
- Find out your identity provider and ensure it allows for OAuth 2.0 Authentication. You will need to know the identity provider url.
- Register a new Web App with your identity provider.
- Provide a Sign In Redirect Url, we recommend https://<your-server>:33332/oauthRedirectUrl
- This will be used in the oauth.redirect.url property
- Provide a Sign Out Redirect Url (Optional but recommended)
- Provide a Sign In Redirect Url, we recommend https://<your-server>:33332/oauthRedirectUrl
How to setup the OAuth Plugin
- Navigate to your 3forge AMI config directory, it's typically located in ami\amione\config
- Create a file called local.properties if one is not already present
- Add the properties from Section 2.2 Minimal Configuration to the file local.properties
- Update the values of the properties to match your identity provider.
- Restart 3forge AMI
Minimal Configuration
Note: Please refer to Section 3 OAuth Full Properties List for a detailed understanding of each property
sso.plugin.class=com.f1.ami.web.AmiWebOAuthPluginImpl
# Provide the url to your OAuth 2.0 identity provider
oauth.server.domain=https://oauthprovider.com
# Provide the redirect url that you configured for the app with your identity provider
oauth.redirect.uri=http://localhost:33332/oauthRedirectUrl
# Provide the endpoints for authorization, token and refresh token
oauth.authorization.endpoint=/authorizeEndpoint
oauth.token.endpoint=/tokenEndpoint
oauth.refresh.token.endpoint=/refreshTokenEndpoint
# Properties related to refresh tokens, redirect uri and scope are optional, by default are set to null
oauth.refresh.redirect.uri=/refreshRedirectUri
oauth.refresh.scope=/refreshScope
oauth.refresh.client.id=/refreshClientId
oauth.refresh.client.secret=/refreshClientSecret
# Provide the client id and secret that will be used for the OAuth authentication
oauth.client.id=clientid
oauth.client.secret=secret
# Replace this with the default scope that is used for Web Based Applications in your firm
oauth.scope=openid profile email offline_access
# Replace this with unique identifier that identifies the user
oauth.username.field=email
# Recommended to replace this with an attribute that identifies the group a user belongs to
oauth.ami.isdev.field=email
oauth.ami.isdev.values=<comma_delimited_list_of_emails>
# Logout Page AMI will display when logged out
web.logged.out.url=/loggedout.htm
# This is enabled for development, disable this after OAuth has been setup
oauth.debug=true
OAuth Full Properties List
| Description | Property and Default Value |
|---|---|
| REQUIRED Specify class to use Oauth SSO |
sso.plugin.class=com.f1.ami.web.AmiWebOAuthPluginImpl |
| REQUIRED The domain of the auth server account |
oauth.server.domain=https://oauthprovider.com |
| REQUIRED Set AMI logged out page |
web.logged.out.url=/loggedout.htm |
| REQUIRED 3forge AMI Url for Oauth server to redirect after login |
oauth.redirect.uri=http://localhost:33332/oauthRedirectUrl/ |
| REQUIRED Client ID |
oauth.client.id=clientid |
| REQUIRED Client secret |
oauth.client.secret=secret |
| REQUIRED Authorization endpoint |
oauth.authorization.endpoint=/authorizeEndpoint |
| REQUIRED Token endpoint |
oauth.token.endpoint=/tokenEndpoint |
| REQUIRED Oauth scope |
oauth.scope=openid profile email offline_access |
| REQUIRED User Email |
oauth.username.field=email |
| OPTIONAL The endpoint to get the refresh token |
oauth.refresh.token.endpoint=/refreshTokenEndpoint |
| OPTIONAL The refresh redirect uri, by default is null, can be overriden |
oauth.refresh.redirect.uri=/refreshRedirectUri |
| OPTIONAL The refresh scope, by default is null,can be overriden |
oauth.refresh.scope=/refreshScope |
| OPTIONAL The client Id after refresh, by default is the same as oauth.client.id,can be overriden |
oauth.refresh.client.id=/refreshClientId |
| OPTIONAL The client Sercret after refresh, by default is the same as oauth.client.secret,can be overriden |
oauth.refresh.client.secret=/refreshClientSecret |
| OPTIONAL Dev User Email |
oauth.ami.isdev.field=email |
| OPTIONAL List of dev user emails |
oauth.ami.isdev.values=<comma_delimited_list_of_emails> |
| OPTIONAL Key that contains the time the access token expires in |
oauth.access.token.expires.in=expires_in |
| OPTIONAL Code challenge method |
oauth.code.challenge.method=S256 |
| OPTIONAL Java hashing algorithm |
oauth.digest.algo=SHA-256 |
| OPTIONAL Seconds to check refresh token expiration |
oauth.session.check.period.seconds=60 |
| OPTIONAL The 3forge AMI endpoint that triggers the build auth request. |
ami.web.index.html.file=index2.htm |
| OPTIONAL Enables Debugging Mode |
oauth.debug=true |
| OPTIONAL Disables certificate validation (for ssl) |
oauth.validate.certs=false |
Creating your own AMI OAuth Plugin
The AMI OAuth plugin handles authorization code and access token requests that are needed for Authenticating to AMI. By extending the 3forge AMI OAuth plugin, you can create your own Ami OAuth Plugin if you have custom requirements for access control or entitlements.
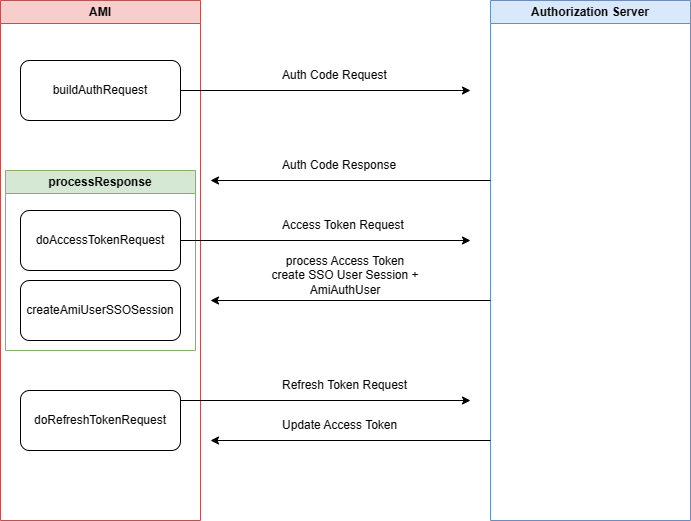
There are three main components to the 3forge AMI OAuth Plugin: buildAuthRequest, processResponse, and createAmiUserSSOSession.
Main Components of the 3forge AMI OAuth Plugin
The buildAuthRequest method is responsible for creating the url for the Authorization Code request.
The processResponse method is responsible for processing the response from the Authorization Code request, then building an Access Token request. Once it obtains an access token, it needs to return an AmiAuthUser.
The createAmiUserSSOSession is responsible for creating the AmiAuthUser and OAuthSSO Session. The AmiAuthUser can be used to set user session variables or restrict access to layouts. The OAuth Session is accessible in AMIScript by session.getSsoSession().
Diagram of the 3forge AMI OAuth Plugin
Example Java Code
1package com.company.3forge;
2
3
4import java.util.Map;
5import com.f1.ami.web.auth.AmiAuthUser;
6import com.f1.container.ContainerTools;
7import com.f1.http.HttpRequestResponse;
8import com.f1.http.HttpSession;
9import com.f1.suite.web.HttpRequestAction;
10import com.f1.utils.PropertyController;
11
12
13public class AmiWebOAuthPluginSample extends AmiWebOAuthPluginImpl {
14 @Override
15 public void init(ContainerTools tools, PropertyController props) {
16 // This is where you can initialize any properties.
17 super.init(tools, props);
18 String sample = props.getRequired("oauth.sample.property");
19 String sample2 = props.getOptional("oauth.sample2.property", "defaultValue");
20 }
21 @Override
22 public String getPluginId() {
23 return "SampleOAuthPlugin";
24 }
25 @Override
26 public String buildAuthRequest(HttpRequestResponse req) throws Exception {
27 HttpSession session = req.getSession(true);
28 String requestUri = req.getRequestUri(); // This will be your ami.web.index.html.file
29 Map<String, String> header = req.getHeader();
30 Map<String, String> cookies = req.getCookies();
31 Map<String, String> params = req.getParams();
32
33
34 // This is how you can add a cookie to the response
35 String optionalDomain = null;
36 long optionalExpires = 0;
37 req.putCookie("myCookie", "secretCode", optionalDomain, optionalExpires, null);
38
39
40 // This is how you add a header to the response
41 req.putResponseHeader("myHeader", "value");
42
43
44 // This will build an Authorization Code Request
45 String redirectUrlForLogin = super.buildAuthRequest(req);
46 return redirectUrlForLogin;
47 }
48 @Override
49 public String getExpectedResponsePath() {
50 // This returns the login redirect url that is provided to your identity manager, it is used in the buildAuthRequest
51 return super.getExpectedResponsePath();
52 }
53 @Override
54 public AmiAuthUser processResponse(HttpRequestAction req) throws Exception {
55 HttpRequestResponse authorizeResponse = req.getRequest();
56
57
58 // 1| Create access token request
59 Map<String, Object> accessTokenResult = doAccessTokenRequest(authorizeResponse);
60 if (accessTokenResult == null)
61 return null;
62 AmiAuthUser user = createAmiUserSSOSession(authorizeResponse, accessTokenResult);
63
64
65 // You may add your own properties to the AmiAuthUser via the auth attributes
66 Map<String, Object> authAttributes = user.getAuthAttributes();
67
68
69 // The below is the OAuth session which can be accessed via AMIScript through session.getSsoSession() which returns a SsoSession object
70 AmiWebOAuthSsoSession oauthSession = (AmiWebOAuthSsoSession) authAttributes.get(AmiAuthUser.PROPERTY_SSO_SESSION);
71 Map<String, Object> oauthSessionProperties = oauthSession.getProperties();
72 return user;
73 }
74 @Override
75 protected Map<String, Object> doAccessTokenRequest(HttpRequestResponse request) {
76 // TODO Auto-generated method stub
77 // If you need to change how the access token request operates
78 return super.doAccessTokenRequest(request);
79 }
80 @Override
81 protected Map<String, Object> doRefreshTokenRequest(AmiWebOAuthSsoSession ssoSession) {
82 // TODO Auto-generated method stub
83 // If you need to change how the refresh token request operates
84 return super.doRefreshTokenRequest(ssoSession);
85 }
86
87
88}
Example Configuration
sso.plugin.class=com.company.3forge.AmiWebOAuthPluginSample
# Include the same properties you need for the Quick Start Guide
# ...
# Enabling debug for development to help with diagnosing
oauth.debug=true